Fetching Data and Spreading to Remote Location with PhishingFetching Data and Spreading to Remote Location with Phishing
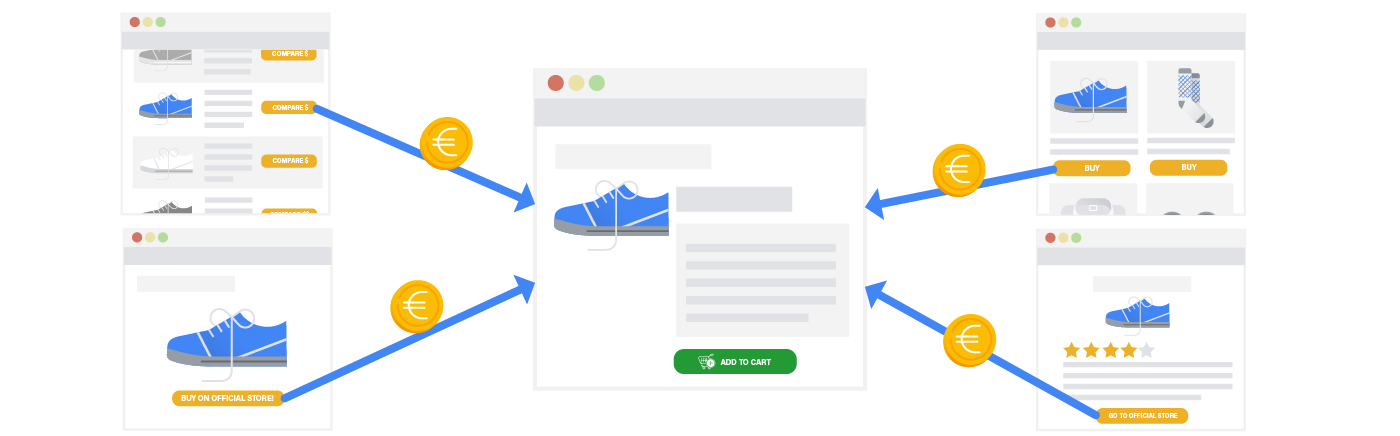
Today there are many typical forms of attacks that different people and organizations use to find the information and facts and personal information of other folks. A webpage that may