Today there are many typical forms of attacks that different people and organizations use to find the information and facts and personal information of other folks. A webpage that may be entirely a copy of the original 1 stimulates individuals to reveal their specifics. Nowadays there are many specialized tools designed for that goal that made it really easy for everybody to spy on other people and get the valuable details that they would like to get. It is really not only the people who utilize various instruments of phishing but businesses and firms also employ it to spy on their own competitors and acquire valuable info about their goods and various statistics in order to take steps on his or her finish to be able to select the greatest strategies which are entirely possible that their firm and enterprise.
Phishing mail is also obtaining very common nowadays and also in it, thieves give an email that appears to be entirely genuine from acompany but to be honest quite the alternative as it is made to catch delicate information.
Distributed Info to Community
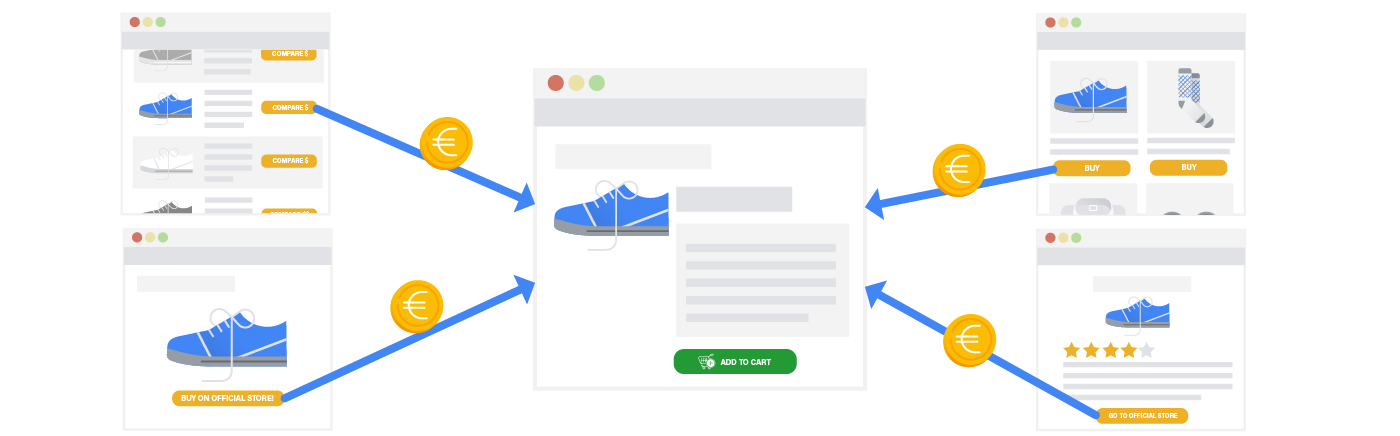
Phishing assaults will not be all about just flooding a particular internet site or possibly a server and receiving a lot of targeted traffic but it’s yet another strategy for scattering hypersensitive info from one provider and relocating it on the group to another spot. Additionally it is typical through the help of fudlink that could be made with any good good quality software program or software these days.
Viruses-Affected Internet pages
There are actually alternative methods phishing episodes could be created right now and one of these is with the aid of viruses-afflicted web pages. This strategy also became very vital and it also functions in a manner that a hacker purchases the advertisement added to an established website. There exists a increased probability that the website visitor will click on that weblink and, by doing this, they get directed to a malware-affected webpage and it also becomes installed on their system or process.